Pixie Dust Attack

WHAT IS WPS
WPS stands for Wi-Fi Protected Setup. It is a network standard created by Cisco in 2006. The main goal of WPS was to make life easier for normal users to set up their own home networks.
Setting up a Wi-Fi Protected Network can sometimes be daunting for less technically knowledgeable users — people who don't really care about how things work as long as it works. WPS was created for such users.
WPS eliminates the need for typing out complex passwords to connect to the network. On devices like televisions which lack an input device, it makes it easier for them to connect to the network.
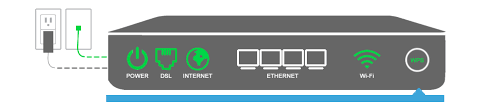
The two most popular methods in WPS are either a WPS push button, where the user pushes a physical button on the back of the router to connect a device — theoretically, anyone with access to the router could log onto the network.
The other method is more secure (but not really), where the user enters an 8-digit pin to connect the device.
This method is the target for Pixie Dust attacks.
THE PIXIE DUST ATTACK
The working of the Pixie Dust attack occurs in two phases:
Handshake Capture
The attacker sends a WPS request to the router. To the router, it looks like an innocent device trying to connect via WPS.
The router and the attacker (the router doesn’t know this) exchange several messages, but the only ones we need are the M1 and M2 messages.
- M1 Message — Sent from the attacker to the router, informing it that the attacker wants to connect. The attacker generates a nonce (random number) and a Diffie-Hellman key pair, then shares the PKe (public key) with the router.
- M2 Message — Sent from the router to the attacker, saying “Okay, let’s connect!”. The M2 message contains the router’s nonce and its PKr (public key).
- The AuthKey is also sent — used to prove the authenticity of the handshake data.
Offline Cryptographic Attack
In this phase, the attacker takes the captured data from the previous step and performs an offline mathematical attack to reconstruct the router’s private key, then uses that to compute the WPS PIN.
This attack relies on the fact that some routers reuse the same private key or generate weak nonces (with poor entropy). Using this, the attacker can brute-force the router’s private key using PKr and the nonce. Each guess is tested against the captured AuthKey from the handshake phase.
If a match is found — the attacker has found the WPS PIN.
DEFENSE AGAINST PIXIE DUST ATTACK
Just disable WPS in your router. LOL.
But again, this comes down to people. Regular users don’t care about this stuff — they lack awareness. As a result, the majority of routers still have WPS enabled.
So, in my opinion, it’s up to the people who set up these networks to properly secure them.